In today’s digital era, email has become a primary communication tool for both personal and professional correspondence. However, this convenience also brings with it a host of cyber threats. Cybercriminals increasingly leverage email to execute a variety of attacks, ranging from spam to sophisticated phishing schemes. Understanding these threats is crucial for protecting sensitive information. This blog post delves into the various types of cyber threats that can infiltrate inboxes, providing insights and guidance on how to mitigate these risks.
Spam

Spam emails, often considered a mere nuisance, can be a gateway to more serious cyber threats. Typically, these unsolicited messages flood inboxes with advertisements, but they can also carry harmful content. Some spam emails are crafted to lure recipients into revealing personal information or clicking on malicious links. The danger lies not just in the annoyance they cause but in their potential to serve as a vector for more damaging cyber attacks, such as malware or phishing attempts.
The risks associated with spam are multifaceted. Beyond cluttering the inbox, spam can slow down email servers and compromise network efficiency. More importantly, some spam emails are cleverly disguised to trick recipients into engaging with harmful content. As the sophistication of these deceptive practices increases, so does the challenge of distinguishing spam from legitimate communication. Vigilance and updated spam filters are crucial in mitigating the risks posed by these unwanted emails.
Malware

Malware, a malicious software designed to damage or disrupt systems, often finds its way into systems via email attachments or embedded links. Once opened or clicked, malware can infect computers, leading to data loss, theft, or even complete system takeover. The varieties of malware range from viruses and worms to trojans and ransomware, each with unique characteristics and impacts. Emails have become a favored tool for malware distribution due to their ability to reach a wide audience quickly.
The impact of malware extends beyond individual inconvenience; it poses a significant threat to organizational security. Malware can compromise sensitive data, disrupt business operations, and result in substantial financial losses. The stealthy nature of some malware makes detection and removal challenging, necessitating robust security measures. Regular updates of antivirus software, cautious handling of unknown email attachments, and employee education are essential steps in protecting against malware distributed through emails.
Data Exfiltration
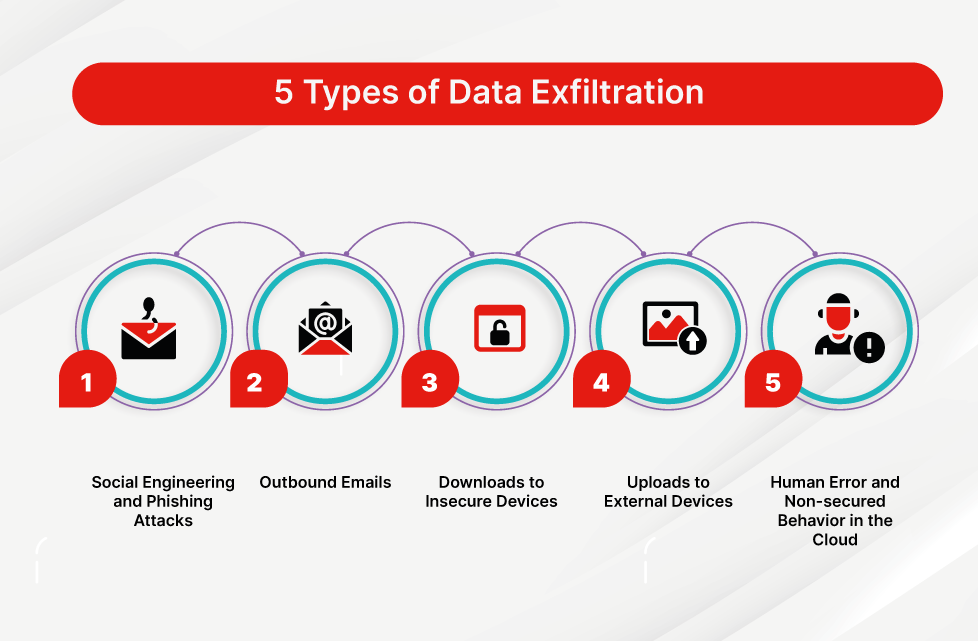
Data exfiltration through email involves unauthorized transfer of sensitive information from a compromised system. Cyber attackers often use sophisticated methods to infiltrate networks and siphon off critical data. These attacks can be executed through malware-infected emails or by gaining direct access to email accounts. Once inside the network, attackers can stealthily extract valuable data over time, leading to significant breaches of privacy and security.
The consequences of such breaches are far-reaching. For individuals, it could mean identity theft or financial loss. For organizations, the ramifications include damage to reputation, loss of customer trust, and potentially hefty legal penalties. Preventing data exfiltration requires a combination of robust cybersecurity measures, employee education, and regular monitoring of network and email activity to detect any unusual patterns that might indicate a breach.


